Your employees are already using AI tools. With Trinity Cyber discover which ones — in minutes.
This is the first in a series on AI governance and security.
Nearly four in five AI-savvy employees use unsanctioned tools at work (Microsoft, 2024). That means shadow AI is already on your network — tools your team adopted with good intentions but without your approval, potentially moving customer data, intellectual property, and source code through services you’ve never evaluated and can’t monitor.
And if your board asks what your AI exposure is today, the honest answer for most security teams is: we don’t know.
In addition to domain-level AI tool detections, our visibility goes further. Trinity Cyber’s SSE 3.0 includes Full Content Inspection™ — technology that automatically removes threats from your live traffic — plus full packet capture (PCAP), giving you the power to discover every shadow AI tool on your network, and see the data flowing through it.
Five questions your AI inventory must answer
If you can answer these five questions with data rather than assumptions, you’re ahead of most of your peers.
1. What AI tools are in use?
2. How are they accessed?
3. Who is using them?
4. How much data is flowing?
5. What’s the risk tier and decision?
Once you can answer these five questions with data rather than assumptions, you have the foundation for an enforceable AI usage policy — one grounded in what’s happening on your network.
See your shadow AI traffic in 15 minutes
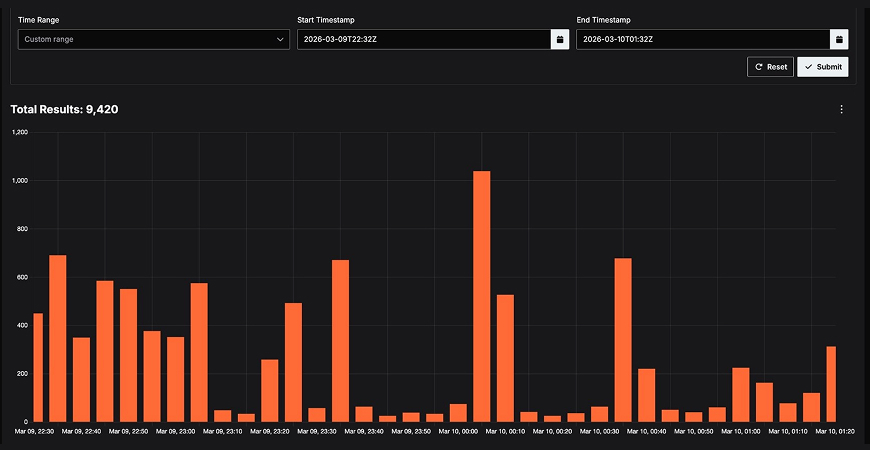
A portion of Pack 1 in action: 9,420 sessions to core LLM services detected in the Trinity Cyber Portal’s Full Session (Advanced PCAP) Search.
AI Detection Packs for the Trinity Cyber Portal
Customers can visit the Trinity Cyber KnowledgeBase for the seven AI Detection Packs noted below. These detection packs let you harness the full power of PCAP searches to illuminate Shadow AI within your network traffic. Each pack searches both encrypted traffic and unencrypted traffic to ensure coverage regardless of how the AI service is accessed.
Seven packs, ordered from highest-signal to broadest coverage:
From visibility to policy — what comes next
Running these packs will likely surface AI usage you didn’t know existed — and that’s the point. A complete inventory transforms shadow AI from an unknown risk into a manageable one. With Trinity Cyber’s unique visibility, you’re seeing what actually crosses your network.