It’s 4:30 on a Friday. The alert hits: Critical VPN vulnerability. Patch immediately. You cancel your evening. You patch the gateway, test connectivity, confirm the fix, and document everything. By the time you’re done, it’s past midnight.
This is the cycle: a critical vulnerability is disclosed, your team scrambles to patch, and the window between disclosure and exploitation gets shorter every year. Over the past two years, remote access VPNs from multiple vendors have suffered pre-authentication bypass and remote code execution vulnerabilities. In many cases, attackers exploited these flaws before a patch was even available. When adversaries move faster than vendors, patching is no longer a defense strategy.
And yet, if your organization is like most, VPN replacement sits on the roadmap as a cloud infrastructure modernization project — important but not urgent. That prioritization costs organizations dearly.
Why VPN Replacement Must Be a Security Priority
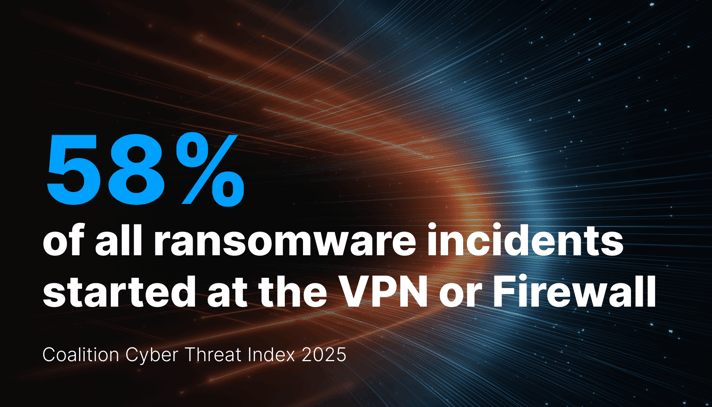
Coalition, a leading cyber insurance provider, reported in its 2025 Cyber Threat Index that 58% of all ransomware incidents started at the VPN or firewall — not email or endpoint. Perimeter gateways — the devices your team is constantly patching — are now the single most exploited entry point in enterprise stacks.
The growing risk reframes the entire conversation. VPN replacement isn’t simply a modernization initiative you can get to next fiscal year. It’s the fast path to reducing your organization’s ransomware risk today. If you need a single compelling statistic that illustrates the risk to your leadership team, it is the 58% figure.
What Most VPN Replacement Projects Get Wrong
Here’s the problem: there is a misconception that replacing your VPN with ZTNA address threat defense.
In fact, ZTNAs were built first for connectivity and access control. They verify the user, check device posture, authorize connections, and create encrypted tunnels between users and applications. Those tunnels are authenticated and trusted. They also completely blind you to threats. A weaponized document travels the same path as a quarterly report. A command-and-control callback rides the same connection as a legitimate API request. The ZTNA verified who connected. Nobody verified what came through.
Both VPNs and competing ZTNAs create encrypted tunnels and cannot see threats. Most ZTNAs leave content uninspected. That is the gap where breaches can begin.
VPN Replacement Done Right: Inspect Content and Connections
What if your ZTNA actually inspected every file, protocol, and line of code flowing through sessions? What if threats were surgically removed from live traffic before they reached your endpoints, and your team never had to triage an alert?
That is exactly what Trinity Cyber delivers. Only Trinity Cyber ZTNA delivers contextual awareness of content. Its threat detections target enduring adversary behaviors. Trinity Cyber even addresses polymorphic malware variants that adversaries create with AI tools. Our patented Full Content Inspection™ (FCI) engine parses live network sessions — files, scripts, protocols — and removes threats in real time with sub-millisecond inspection latency. Your users connect to private applications and the internet seamlessly. They experience a fast, reliable network. Attackers are disarmed. And, your team’s dashboard shows actions taken — not alerts to chase.
Trinity Cyber customers replace their legacy VPNs and modernize remote access without adding headcount or alerts. Our platform, built to defend the world’s most targeted networks, now protects universities, retailers, financial institutions, manufacturers, and more. One customer even had special compliance needs that they met with Trinity Cyber: read the case study.
VPN replacement is the highest-leverage security decision you can make this quarter. Not because VPNs are old technology — because they are the most exploited, and standard ZTNAs don’t close the gap.